<p><strong>简介</strong>原文链接</p>
<p> .net core使用ocelot---第一篇 简单使用</p>
<p> 接上文,我将继续介绍使用asp.net core 创建API网关,重要介绍身份验证(authentication )相关内容。</p>
<p> API服务是需要保护的资源,我们应该尽可能的保证他们的安全。</p>
<p> 通常,我们会使用aspnet security 来保证我们项目的安全,aspnet security代码库是为asp.net core 设计的安全和授权中间件。已经让事情变得简单。</p>
<p> 那么我们在项目中引入API网关会不会导致巨大的改变?答案是,不会。我们的修改微乎其微,但是却让安全和授权变得简单。</p>
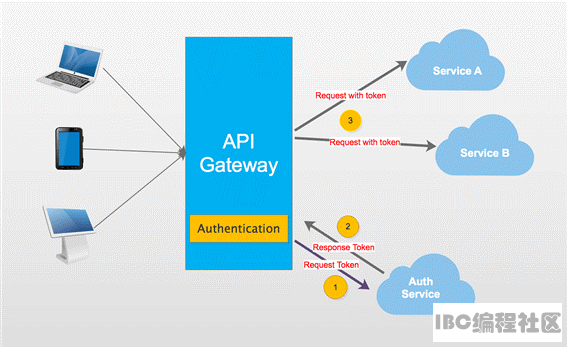
<p> 先看下面的截图。</p>
<p><div align="center">
 </div></p>
</div></p>
<p> 截图显示,当我们访问我们的服务,API网关会让我们首先访问其授权模块。我们必须访问授权服务获得访问令牌(access token),然后用访问令牌访问受保护的服务。</p>
<p> 可能你倾向将授权服务独立,这意味客户端得先访问授权服务获得访问令牌。然后携带令牌访问API网关。毫无疑问这样做没问题,但是我建议将授权服务和其他服务放在一起。</p>
<p> APIGateway是我们所有服务的入口,对于身份未验证的客户端仅可以访问授权服务。</p>
<p> OK,开始我们的表演。</p>
<p> 我会使用上一个demo的部分内容,便于理解。</p>
<p><strong>Step1</strong></p>
<table style="width: 100%;" border="1" cellspacing="0" cellpadding="0">
<tbody>
<tr>
<td>
<p><strong>项目名称</strong></p>
</td>
<td>
<p><strong>项目类型</strong></p>
</td>
<td>
<p>描述</p>
</td>
</tr>
<tr>
<td>
<p>APIGateway</p>
</td>
<td>
<p>ASP.NET Core Empty</p>
</td>
<td>
<p>示例的入口</p>
</td>
</tr>
<tr>
<td>
<p>CustomersAPIServices</p>
</td>
<td>
<p>ASP.NET Core Web API</p>
</td>
<td>
<p>API 服务处理消费者的操作</p>
</td>
</tr>
<tr>
<td>
<p>AuthServer</p>
</td>
<td>
<p>ASP.NET Core Web API</p>
</td>
<td>
<p>API 服务处理授权操作</p>
</td>
</tr>
<tr>
<td>
<p>ClientApp</p>
</td>
<td>
<p>Console App</p>
</td>
<td>
<p>控制台程序模拟客户端</p>
</td>
</tr>
</tbody>
</table>
<p> APIGateway和CustomerAPIServices和上篇文章的例子一样,你可以在APIGatewayBasicDemo获得。</p>
<p><strong>Step2</strong></p>
<p> 创建AuthServer,AuthServer重要是为request请求生成访问令牌(access token),我们需要添加一个方法处理。</p>
- [HttpGet]
- public IActionResult Get(string name, string pwd)
- {
- //just hard code here.
- if (name == "catcher" && pwd == "123")
- {
- var now = DateTime.UtcNow;
-
- var claims = new Claim[]
- {
- new Claim(JwtRegisteredClaimNames.Sub, name),
- new Claim(JwtRegisteredClaimNames.Jti, Guid.NewGuid().ToString()),
- new Claim(JwtRegisteredClaimNames.Iat, now.ToUniversalTime().ToString(), ClaimValueTypes.Integer64)
- };
-
- var signingKey = new SymmetricSecurityKey(Encoding.ASCII.GetBytes(_settings.Value.Secret));
- var tokenValidationParameters = new TokenValidationParameters
- {
- ValidateIssuerSigningKey = true,
- IssuerSigningKey = signingKey,
- ValidateIssuer = true,
- ValidIssuer = _settings.Value.Iss,
- ValidateAudience = true,
- ValidAudience = _settings.Value.Aud,
- ValidateLifetime = true,
- ClockSkew = TimeSpan.Zero,
- RequireExpirationTime = true,
-
- };
-
- var jwt = new JwtSecurityToken(
- issuer: _settings.Value.Iss,
- audience: _settings.Value.Aud,
- claims: claims,
- notBefore: now,
- expires: now.Add(TimeSpan.FromMinutes(2)),
- signingCredentials: new SigningCredentials(signingKey, SecurityAlgorithms.HmacSha256)
- );
- var encodedJwt = new JwtSecurityTokenHandler().WriteToken(jwt);
- var responseJson = new
- {
- access_token = encodedJwt,
- expires_in = (int)TimeSpan.FromMinutes(2).TotalSeconds
- };
-
- return Json(responseJson);
- }
- else
- {
- return Json("");
- }
- }
<p> 在验证用户时。我使用硬编码将用户名写死,由于对于本文这个不是那么重要。</p>
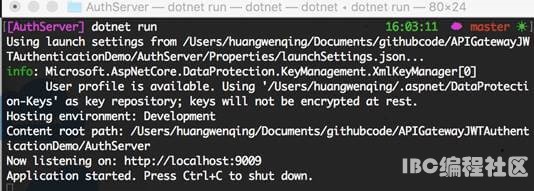
<p> 这样我们就完成了授权服务,现在跑起来。</p>
<p><div align="center">
 </div></p>
</div></p>
<p><strong>Step3</strong></p>
<p> 回到CustomersAPIServices项目,我们应该保护这个服务。</p>
<p> 修改Startup,我们可以使用授权。在这我用JwtBearer进行授权,我会给TestKey设置默认的授权方案。TestKey我将在下面提到。</p>
- public void ConfigureServices(IServiceCollection services)
- {
- var audienceConfig = Configuration.GetSection("Audience");
-
- var signingKey = new SymmetricSecurityKey(Encoding.ASCII.GetBytes(audienceConfig["Secret"]));
- var tokenValidationParameters = new TokenValidationParameters
- {
- ValidateIssuerSigningKey = true,
- IssuerSigningKey = signingKey,
- ValidateIssuer = true,
- ValidIssuer = audienceConfig["Iss"],
- ValidateAudience = true,
- ValidAudience = audienceConfig["Aud"],
- ValidateLifetime = true,
- ClockSkew = TimeSpan.Zero,
- RequireExpirationTime = true,
- };
-
- services.AddAuthentication()
- .AddJwtBearer("TestKey", x =>
- {
- x.RequireHttpsMetadata = false;
- x.TokenValidationParameters = tokenValidationParameters;
- });
-
- services.AddMvc();
- }
- public void Configure(IApplicationBuilder app)
- {
- app.UseAuthentication();
- app.UseMvc();
- }
<p> 接下来,对需要保护的方法,添加Authorize。</p>
- [Authorize]
- [HttpGet]
- public IEnumerable<string> Get()
- {
- return new string[] { "Catcher Wong", "James Li" };
- }
<p><strong>注意</strong></p>
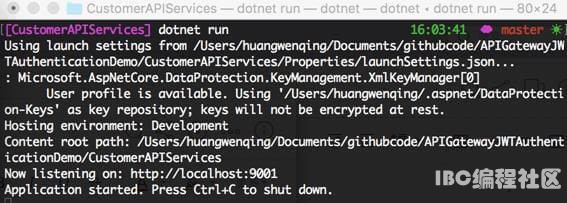
<p> 该项目基于asp.net core 2.0. 如果你的项目是1.X,可能有些不同,建议用迁移迁移到2.0.以上。接下来就是见证奇迹的时候了。</p>
<p><div align="center">
 </div></p>
</div></p>
<p><strong>Step4</strong></p>
<p> 最重要的步骤来了,在APIGateway中配置授权。</p>
- public void ConfigureServices(IServiceCollection services)
- {
- var audienceConfig = Configuration.GetSection("Audience");
-
- var signingKey = new SymmetricSecurityKey(Encoding.ASCII.GetBytes(audienceConfig["Secret"]));
- var tokenValidationParameters = new TokenValidationParameters
- {
- ValidateIssuerSigningKey = true,
- IssuerSigningKey = signingKey,
- ValidateIssuer = true,
- ValidIssuer = audienceConfig["Iss"],
- ValidateAudience = true,
- ValidAudience = audienceConfig["Aud"],
- ValidateLifetime = true,
- ClockSkew = TimeSpan.Zero,
- RequireExpirationTime = true,
- };
-
- services.AddAuthentication()
- .AddJwtBearer("TestKey", x =>
- {
- x.RequireHttpsMetadata = false;
- x.TokenValidationParameters = tokenValidationParameters;
- });
-
- services.AddOcelot(Configuration);
- }
<p> </p>
<p> 这个配置的大部分代码和Customer Service一样。</p>
<p> 当Ocelot启动,它会检察ReRoutes 》AuthenticationOptions 》AuthenticationProviderKey 的值,</p>
<p>检查该值是否被授权服务注册,如果没有,Ocelot不会启动,如果有,Ocelot在实行时使用授权服务。</p>
<p> 所以,我们得修改configuration.json,我们需要添加新的节点,并将其值赋为在Startup 类中定义的一样。</p>
- {
- "DownstreamPathTemplate": "/api/customers",
- "DownstreamScheme": "http",
- "DownstreamHost": "localhost",
- "DownstreamPort": 9001,
- "UpstreamPathTemplate": "/customers",
- "UpstreamHttpMethod": [ "Get" ],
- "AuthenticationOptions": {
- "AuthenticationProviderKey": "TestKey",
- "AllowedScopes": []
- }
- }
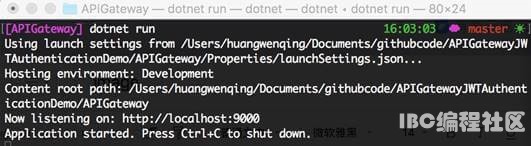
<p> 启动服务。</p>
<p style="margin-left: 18.0pt;"> </p>
<p><div align="center">
 </div></p>
</div></p>
<p ><strong>注意</strong></p>
<p > 当你启动项目时遇到下面的错误,你应该检查你的代码,检察AddJwtBearer 方法是否指明授权方案。</p>
<p ><em> Unhandled Exception: System.InvalidOperationException: Scheme already exists: Bearer</em></p>
<p ><em>Step5</em></p>
<p > 我们已经准备完毕,我们用我们的客户端模拟APIGateway的某些请求。</p>
<p> </p>
<p > 我们先添加获得访问令牌的方法。</p>
- private static string GetJwt()
- {
- HttpClient client = new HttpClient();
- client.BaseAddress = new Uri( "http://localhost:9000");
- client.DefaultRequestHeaders.Clear();
- var res2 = client.GetAsync("/api/auth?name=catcher&pwd=123").Result;
- dynamic jwt = JsonConvert.DeserializeObject(res2.Content.ReadAsStringAsync().Result);
- return jwt.access_token;
- }
<p> </p>
<p style="margin-left: 18.0pt;"> 接下来,编写通过APIGateway访问Customer Service方法的代码。</p>
- static void Main(string[] args)
- {
- HttpClient client = new HttpClient();
-
- client.DefaultRequestHeaders.Clear();
- client.BaseAddress = new Uri("http://localhost:9000");
-
- // 1. without access_token will not access the service
- // and return 401 .
- var resWithoutToken = client.GetAsync("/customers").Result;
-
- //print something here
-
- //2. with access_token will access the service
- // and return result.
- client.DefaultRequestHeaders.Clear();
- var jwt = GetJwt();
-
- client.DefaultRequestHeaders.Add("Authorization", $"Bearer {jwt}");
- var resWithToken = client.GetAsync("/customers").Result;
-
- //print something here
-
- //3. visit no auth service
- client.DefaultRequestHeaders.Clear();
- var res = client.GetAsync("/customers/1").Result;
-
- //print something here
-
- Console.Read();
- }
<p> </p>
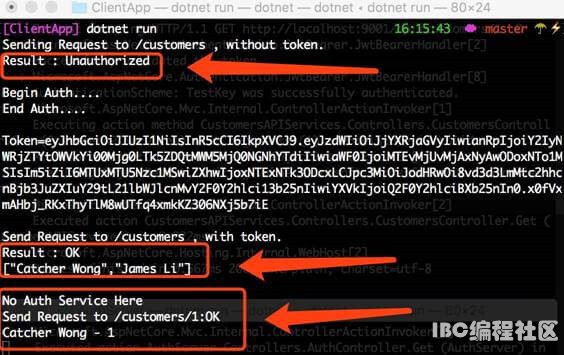
<p style="margin-left: 18.0pt;">运行结果。</p>
<p style="margin-left: 18.0pt;"><div align="center">
 </div></p>
</div></p>
<p style="margin-left: 18.0pt;"> </p>
<p> 完工。</p>
<p> 源码在此。</p>
<p><strong>总结</strong></p>
<p> 没啥。</p>
<p> </p><br>来源:<a href="https://www.cnblogs.com/xlxr45/p/11321134.html" target="_blank">https://www.cnblogs.com/xlxr45/p/11321134.html</a><br>免责声明:如果侵犯了您的权益,请联系站长,我们会及时删除侵权内容,谢谢合作! |